Phishing
The fraudulent practice of sending emails pretending to be from reputable companies in order to induce individuals to reveal personal information, such as passwords and credit card numbers.

Social Engineering
Is the art of manipulating people so they give up confidential information. When individuals are targeted the criminals are usually trying to trick you into giving them your passwords or bank information, or access your computer to secretly install malicious software–that will give them access to your passwords and bank information as well as giving them control over your computer.
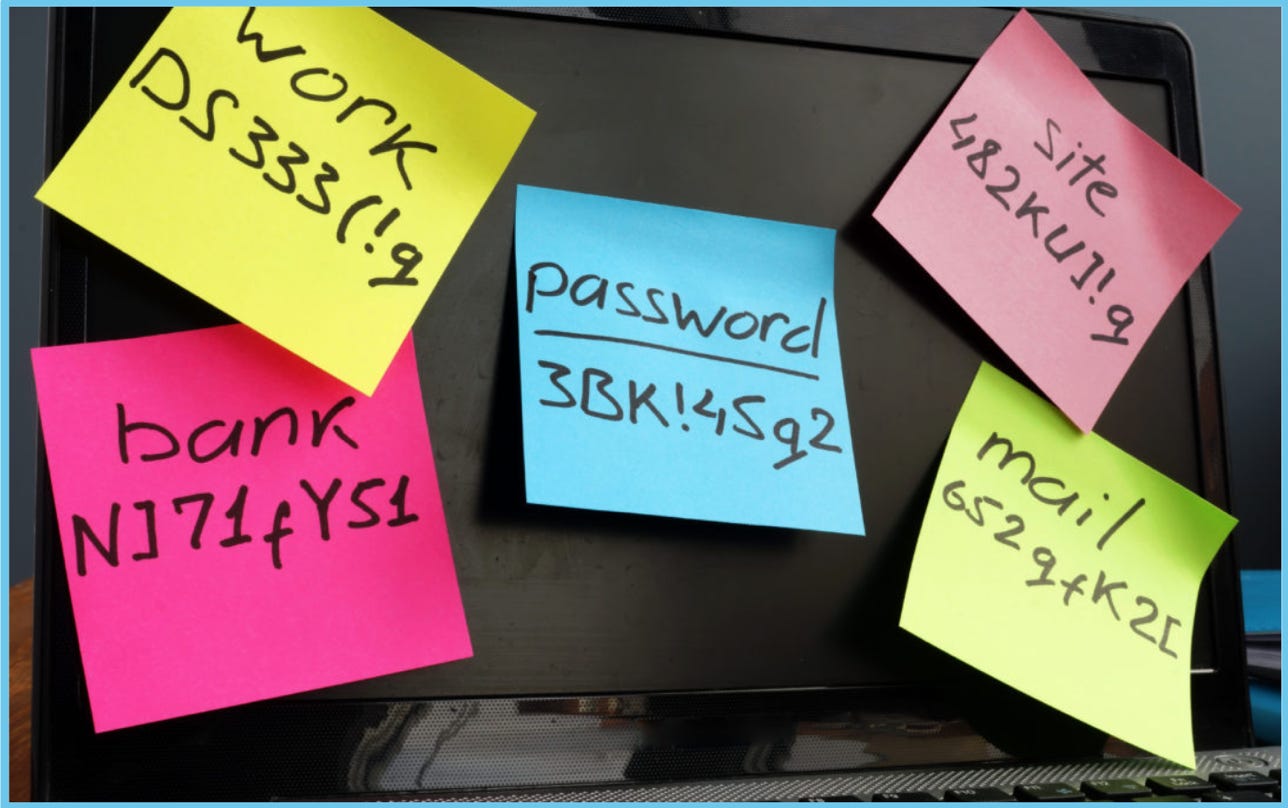
Passwords best practices
Never reveal your passwords to others
Use different passwords for different accounts and websites
Use Two-factor authentication
Use Length & complexity
Make passwords that are hard to guess but easy to remember
Use a password manager
Don’t write passwords in stickies
Cybersecurity Best Practices
Office
Computer
- Physical security, access and locks to IT communication equipment (MDF and IDF)
- Proper Firewall equipment and configurations
- Content Filters and Traffic Shaping rules
- Access Points (WIFI) with proper configuration and passphrase, avoid open WiFi
- Backups
- Guest WiFi for external users
- User CyberSecurity Training
- DNS (Umbrella) & SPAM (CPL) Protection is a plus

